Remote IoT SSH free download is a growing necessity for businesses and individuals seeking to manage their Internet of Things (IoT) devices securely and efficiently. As IoT devices become more integrated into daily life, the ability to remotely access and manage them is crucial. In this article, we will explore the significance of remote IoT SSH, its benefits, and how you can download and implement it for free.
IoT technology has revolutionized the way we interact with devices. From smart homes to industrial automation, IoT devices are transforming industries. However, managing these devices remotely requires secure solutions. Remote IoT SSH offers a secure tunnel to connect to your devices, ensuring data integrity and protecting against cyber threats.
This guide will provide you with an in-depth understanding of remote IoT SSH, including step-by-step instructions, best practices, and tools to download and use it effectively. Whether you're a beginner or an advanced user, this article will equip you with the knowledge you need to leverage remote IoT SSH for your projects.
Table of Contents
- Introduction to Remote IoT SSH
- Benefits of Remote IoT SSH
- How Remote IoT SSH Works
- Tools for Remote IoT SSH
- Setting Up Remote IoT SSH
- Security Considerations
- Free Download Options
- Troubleshooting Common Issues
- Best Practices for Remote IoT SSH
- Conclusion
Introduction to Remote IoT SSH
Remote IoT SSH (Secure Shell) is a protocol designed to provide secure communication between IoT devices and remote users. This protocol encrypts data transmitted between devices and servers, ensuring confidentiality and integrity. With remote IoT SSH, you can manage your IoT devices from anywhere in the world, as long as you have an internet connection.
Why Use Remote IoT SSH?
The primary reason for using remote IoT SSH is security. Unlike traditional methods, SSH encrypts all data transferred between devices, making it difficult for hackers to intercept sensitive information. Additionally, SSH supports authentication mechanisms, ensuring only authorized users can access your IoT devices.
Benefits of Remote IoT SSH
Implementing remote IoT SSH offers numerous advantages for both personal and professional use cases. Below are some key benefits:
- Enhanced Security: Protect your IoT devices from unauthorized access and cyber threats.
- Remote Access: Manage your devices from anywhere, at any time, without physical presence.
- Cost-Effective: Eliminate the need for expensive hardware or proprietary solutions.
- Scalability: Easily scale your IoT infrastructure as your needs grow.
How Remote IoT SSH Works
Remote IoT SSH operates by establishing a secure tunnel between your local machine and the IoT device. This tunnel encrypts all data transmitted, ensuring it remains private and secure. The process involves:
- Connecting to the IoT device using an SSH client.
- Authenticating the user through passwords or public key authentication.
- Transferring encrypted data between the devices.
Key Components of Remote IoT SSH
Understanding the key components of remote IoT SSH is essential for effective implementation:
- SSH Client: Software used to initiate the connection.
- SSH Server: Software running on the IoT device to accept incoming connections.
- Encryption Algorithms: Protocols used to secure data transmission.
Tools for Remote IoT SSH
Several tools are available for implementing remote IoT SSH. Below are some popular options:
1. PuTTY
PuTTY is a widely used SSH client for Windows users. It offers a simple interface and supports various protocols, including SSH.
2. OpenSSH
OpenSSH is a free and open-source SSH client and server software. It is commonly used on Linux and macOS systems.
3. MobaXterm
MobaXterm is an advanced SSH client that includes additional features such as file transfer and terminal emulation.
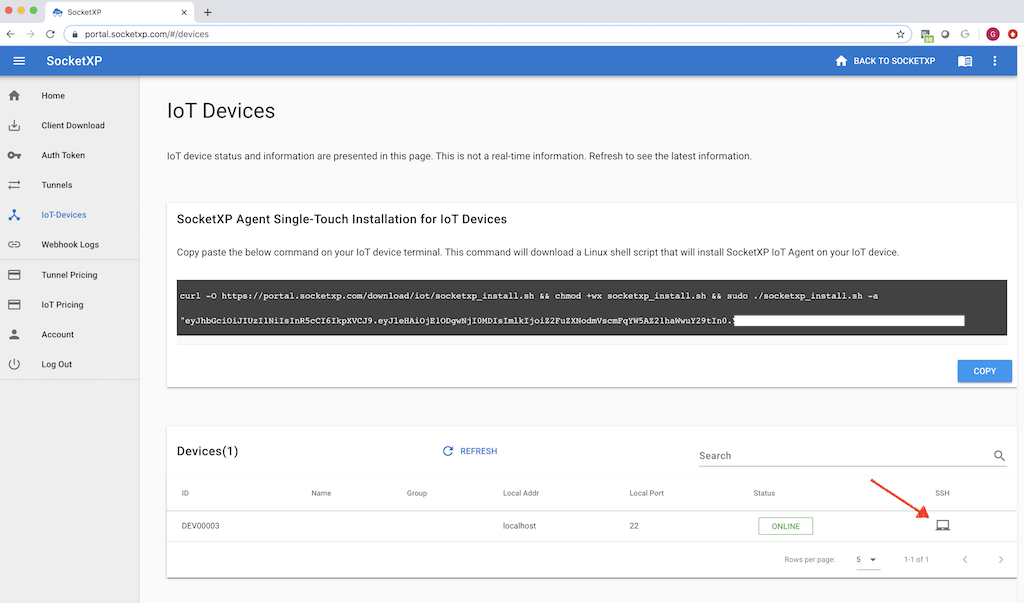
Setting Up Remote IoT SSH
Setting up remote IoT SSH involves several steps. Follow the guide below to configure your system:
Step 1: Install SSH Server on IoT Device
Ensure your IoT device has an SSH server installed. For Linux-based devices, you can use OpenSSH:
Run the following command to install OpenSSH:
sudo apt-get install openssh-server
Step 2: Configure Firewall Settings
Allow incoming SSH connections by configuring your firewall:
sudo ufw allow ssh
Step 3: Connect Using SSH Client
Use an SSH client like PuTTY or OpenSSH to connect to your IoT device. Enter the IP address and port number to establish the connection.
Security Considerations
While remote IoT SSH enhances security, it is essential to follow best practices to maximize protection:
- Use Strong Passwords: Avoid using easily guessable passwords.
- Implement Public Key Authentication: Use SSH keys for added security.
- Regularly Update Software: Keep your SSH client and server software up to date.
Free Download Options
Several platforms offer free downloads for remote IoT SSH tools. Below are some reputable sources:
1. Official OpenSSH Website
Visit the OpenSSH website to download the latest version of OpenSSH for free.
2. PuTTY Download Page
Download PuTTY from its official website for Windows users.
3. MobaXterm Free Edition
Access the free edition of MobaXterm from their official site.
Troubleshooting Common Issues
Encountering issues while setting up remote IoT SSH is common. Below are solutions to some frequent problems:
Problem: Unable to Connect
Solution: Verify the IP address and port number. Ensure the SSH server is running on the IoT device.
Problem: Authentication Failure
Solution: Double-check your username and password. If using SSH keys, ensure the public key is correctly added to the authorized_keys file.
Best Practices for Remote IoT SSH
Adopting best practices ensures optimal performance and security:
- Limit Access: Restrict SSH access to trusted IP addresses.
- Monitor Activity: Regularly review logs to detect suspicious activities.
- Backup Configuration: Keep backups of your SSH configurations to prevent data loss.
Conclusion
Remote IoT SSH free download offers a secure and efficient way to manage your IoT devices remotely. By following the guidelines outlined in this article, you can set up and utilize remote IoT SSH effectively. Remember to prioritize security and adhere to best practices to protect your devices from potential threats.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more insights into IoT and related technologies. Together, let's build a safer and smarter connected world!