Connecting remotely to your IoT devices is essential in today's interconnected world. Whether you're managing smart home systems, industrial automation, or personal projects, setting up a remote IoT platform via SSH on a Raspberry Pi without MAC (Media Access Control) address exposure is critical for security and privacy. This guide will walk you through every step of the process, ensuring your IoT setup remains secure, efficient, and accessible from anywhere.
As the demand for remote access grows, so does the need for secure and reliable solutions. Remote IoT platforms allow users to monitor, manage, and control devices from a distance, but it’s important to implement best practices to protect your network. SSH (Secure Shell) provides an encrypted connection, making it ideal for remote management.
This article will explore how to set up a remote IoT platform using SSH on a Raspberry Pi without exposing your MAC address, covering essential steps, troubleshooting tips, and security best practices. Whether you're a beginner or an experienced developer, this guide will provide valuable insights to enhance your IoT projects.
Understanding Remote IoT Platforms
Before diving into the technical aspects, it's important to understand what a remote IoT platform entails. An IoT platform serves as the backbone of any connected system, enabling communication between devices, data collection, and remote control. For remote access, SSH is one of the most secure protocols available.
Key Features of Remote IoT Platforms
- Secure communication between devices and servers
- Centralized management of multiple devices
- Data encryption to protect sensitive information
- Scalability for growing IoT ecosystems
When setting up a remote IoT platform, security should be your top priority. Exposing MAC addresses can compromise your network, which is why this guide emphasizes secure configurations.
Why Use SSH for Remote IoT Platforms?
SSH (Secure Shell) is a cryptographic network protocol designed for secure communication over unsecured networks. It provides a secure channel for accessing remote systems, transferring files, and executing commands. Here’s why SSH is ideal for remote IoT platforms:
- End-to-end encryption ensures data remains private
- Authentication mechanisms prevent unauthorized access
- Supports secure file transfers via SCP (Secure Copy Protocol)
SSH is widely supported across operating systems, making it accessible for most users. By using SSH, you can remotely manage your Raspberry Pi and IoT devices without worrying about data interception.
Setting Up SSH on Raspberry Pi
Step-by-Step Guide
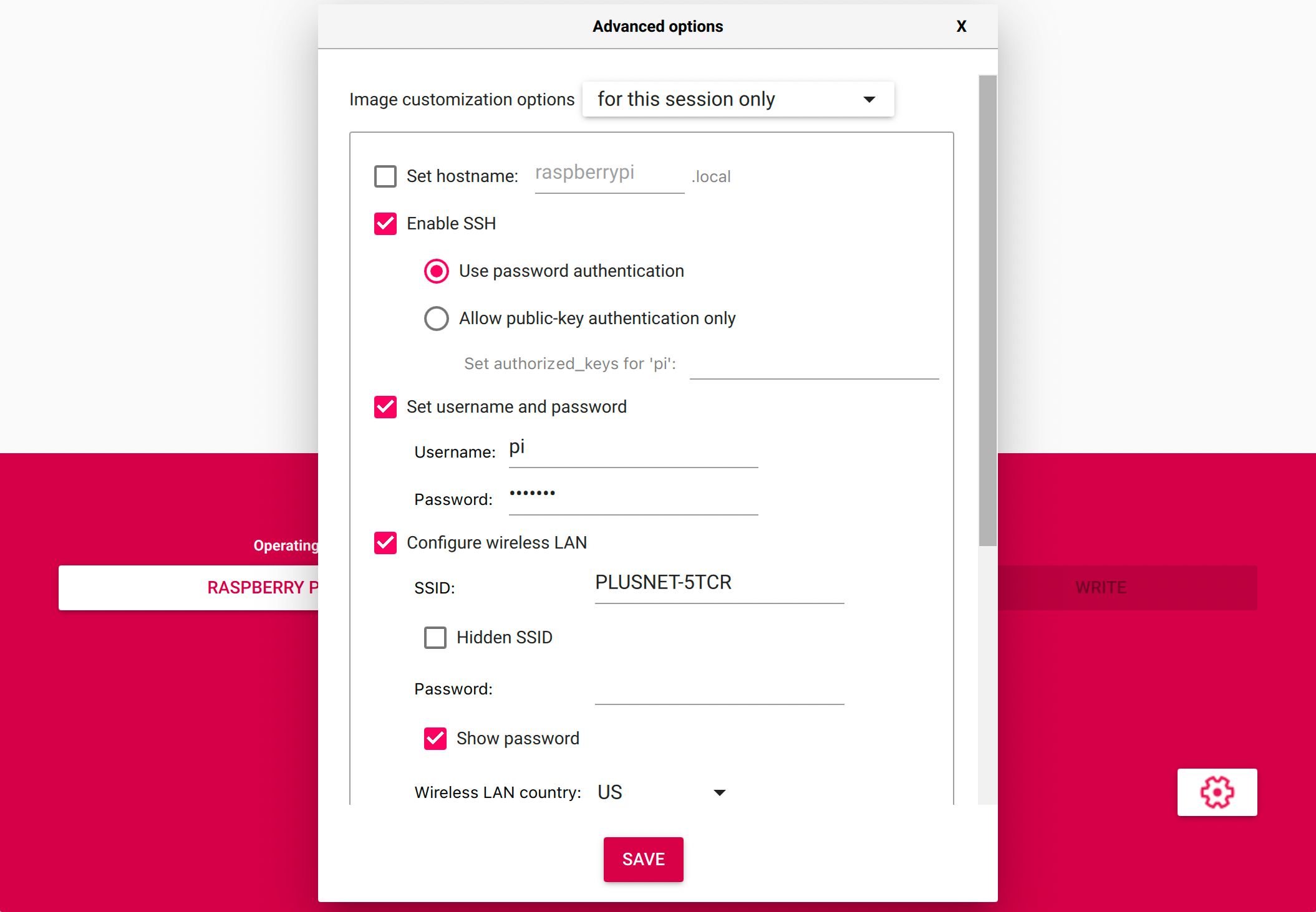
Setting up SSH on a Raspberry Pi involves several straightforward steps. Follow this guide to ensure a secure and functional setup:
- Download the latest version of Raspberry Pi OS from the official website
- Flash the image to an SD card using a tool like Balena Etcher
- Enable SSH by creating an empty file named "ssh" in the boot partition
- Insert the SD card into your Raspberry Pi and power it on
- Connect to the Raspberry Pi via Ethernet or Wi-Fi
- Use an SSH client (e.g., PuTTY or Terminal) to connect to the device
Once connected, you can begin configuring your Raspberry Pi for remote access. This setup ensures SSH is enabled and ready for use.
Securing Your Raspberry Pi Without MAC Address Exposure
MAC addresses are unique identifiers assigned to network interfaces. While they are essential for network communication, exposing them can lead to security vulnerabilities. Here’s how to prevent MAC address exposure:
Techniques to Hide MAC Addresses
- Use a static IP address instead of DHCP
- Enable MAC address randomization in your Wi-Fi settings
- Configure a firewall to restrict incoming connections
By implementing these techniques, you can enhance the security of your Raspberry Pi and protect your network from unauthorized access.
Downloading Remote IoT Platform Software
Once SSH is configured, you’ll need to download and install the necessary software for your remote IoT platform. Here’s a list of popular options:
- Node-RED: A flow-based programming tool for IoT applications
- Mosquitto: An open-source MQTT broker for messaging
- InfluxDB: A time-series database for data storage
- Grafana: A visualization tool for monitoring IoT data
These tools work seamlessly with Raspberry Pi and can be installed via the command line using package managers like apt.
Troubleshooting Common Issues
Setting up a remote IoT platform can sometimes encounter challenges. Here are some common issues and their solutions:
Issue 1: SSH Connection Refused
If you receive an "SSH connection refused" error, ensure the following:
- SSH is enabled on your Raspberry Pi
- The correct IP address is used for the connection
- Firewall rules allow SSH traffic (port 22)
Issue 2: MAC Address Not Hiding
If your MAC address is still visible, double-check the following:
- MAC address randomization is enabled in your Wi-Fi settings
- A static IP address is configured correctly
Troubleshooting these issues ensures a smooth setup process.
Best Practices for Remote IoT Platforms
Implementing best practices is crucial for maintaining a secure and efficient remote IoT platform. Here are some recommendations:
- Use strong, unique passwords for SSH access
- Regularly update your Raspberry Pi and installed software
- Monitor network activity for suspicious behavior
- Document your setup process for future reference
Following these practices will help safeguard your IoT devices and ensure reliable remote access.
Security Considerations for Remote IoT Platforms
Security should always be a priority when managing remote IoT platforms. Here are some key considerations:
Data Encryption
Ensure all data transmitted between devices is encrypted using protocols like SSH or TLS. This prevents eavesdropping and data interception.
User Authentication
Implement multi-factor authentication (MFA) to add an extra layer of security. This reduces the risk of unauthorized access even if credentials are compromised.
Regular Audits
Conduct regular security audits to identify and address vulnerabilities. This proactive approach helps maintain the integrity of your IoT platform.
Case Studies: Real-World Applications
Remote IoT platforms have numerous applications across various industries. Here are a few examples:
Smart Agriculture
Farmers use IoT sensors to monitor soil moisture, temperature, and humidity levels. By connecting these sensors to a remote platform, they can make data-driven decisions to optimize crop yields.
Industrial Automation
Manufacturers leverage IoT platforms to monitor production lines and equipment performance. Remote access enables engineers to troubleshoot issues and perform maintenance without being physically present.
Smart Homes
Homeowners use IoT devices to control lighting, thermostats, and security systems. A remote platform allows them to manage their smart home ecosystem from anywhere in the world.
Future Trends in Remote IoT Platforms
The IoT industry continues to evolve, with new technologies and innovations emerging regularly. Here are some trends to watch:
- Edge computing for faster data processing
- AI-driven analytics for predictive maintenance
- 5G networks for improved connectivity
Staying informed about these trends will help you leverage the full potential of remote IoT platforms in the future.
Conclusion
In conclusion, setting up a remote IoT platform using SSH on a Raspberry Pi without exposing your MAC address is both feasible and secure. By following the steps outlined in this guide, you can create a robust and reliable system for managing your IoT devices. Remember to prioritize security, implement best practices, and stay updated with the latest trends in the IoT industry.
We encourage you to share your thoughts and experiences in the comments section below. If you found this article helpful, consider sharing it with others who may benefit from the information. For more in-depth guides and tutorials, explore our other articles on IoT and Raspberry Pi projects.
Table of Contents
- Understanding Remote IoT Platforms
- Why Use SSH for Remote IoT Platforms?
- Setting Up SSH on Raspberry Pi
- Securing Your Raspberry Pi Without MAC Address Exposure
- Downloading Remote IoT Platform Software
- Troubleshooting Common Issues
- Best Practices for Remote IoT Platforms
- Security Considerations for Remote IoT Platforms
- Case Studies: Real-World Applications
- Future Trends in Remote IoT Platforms